Robustness-as-Traceability: Secure and Legal Calibration Workflows in IoT (RoasT-IoT)
RoasT-IoT’s vision is to enable all sensed data and actuation on IoT platforms to be anonymously traced back to securely calibrated sensors whilst ensuring that anonymity can be stripped back if legal problems occur.
Sensing accuracy is a key requirement in safety-critical IoT deployments. Calibration plays an important role in ensuring device accuracy. Consequently, the security of calibration processes is an important security requirement — an uncalibrated deployment cannot be expected to work correctly with negative legal consequences. In turn, this can lead to failures which may trigger safety or security legislation as well, potentially leading to criminal or civil liability.
To control IoT workflows and to achieve assurance requirements and legal compliance, users need visibility into workflows and the ability to exclude compromised or poorly calibrated devices. RoasT-IoT’s objective is to provide security and legal contexts to data generated within an IoT ecosystem about what devices, sensors, and ML applications that data has been exposed to.
RoasT-IoT will also develop tools to reason about the security properties of the workflow context whilst balancing operator privacy with user security requirements, and relevant legal obligations. These deliverables will bootstrap context-based access control and enforcement based on the contextual characteristics of the data such as provenance, calibration, and specific devices or applications, along with what users should and should not do in accordance with relevant legal requirements applicable to IoT devices and calibration trails broadly conceived. RoasT-IoT contributes to cybersecurity of IoT by considering both legal and technical challenges around workflow traceability, focusing on the dual lenses of Internet (of Things) law and Security-at-the-Edge.
The publications of this project span technical papers in encryption and privacy in IoT and robot operations, legal analysis of both the market which RoasT-IoT devices find themselves in, and which types of actions must be taken by our societies to best use and prevent misuse of the IoT area in general. These all implement the goals set forth above in a technical, societal, and legal sense.
Outputs:
Published Papers
Oles Andriychuk, Shishir Nagaraja, “Regulating Digital Advertising from the Perspective of the 4th Industrial Revolution”, in Moura Vincente, Sofia de Vasconcelos Casimiro (eds), ‘The Legal Challenges of the Fourth Industrial Revolution: the European Union’s Digital Strategy’, Springer, 2023
Ludvigsen, Nagaraja, Daly, Preventing or Mitigating Adversarial Supply Chain Attacks: A Legal Analysis, ACM CCS, SCORED’ 22, https://dl.acm.org/doi/10.1145/3560835.3564552, 2022.
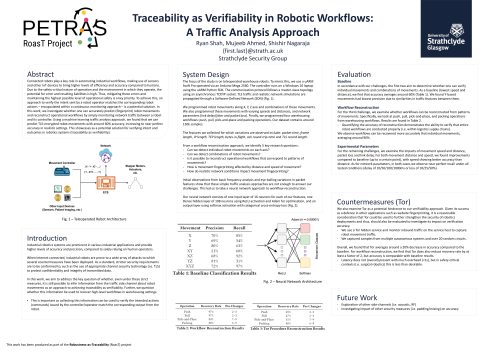
Ryan Shah, Mujeeb Ahmed, Shishir Nagaraja, Can You Still See Me?: Identifying Robot Operations Over End-to-End Encrypted Channels, Proceedings of the 15th ACM Conference on Security and Privacy in Wireless and Mobile Networks, https://doi.org/10.1145/3507657.3529659, 2022.
Preprints
Oles Andriychuk, Shishir Nagaraja, “The Digital Markets Act Amendments: Be Careful What You Wish For” (Proposal stage)
Ludvigsen, Nagaraja, Daly, The Dangers of Computational Law and Cybersecurity; Perspectives from Engineering and the AI Act, http://arxiv.org/abs/2207.00295, 2022.
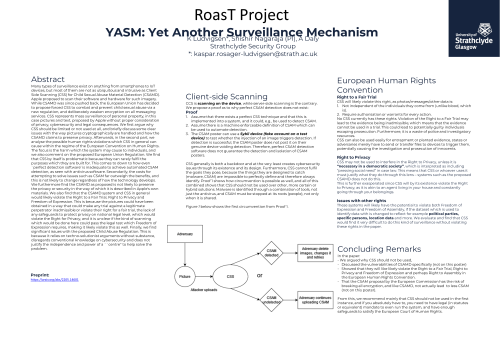
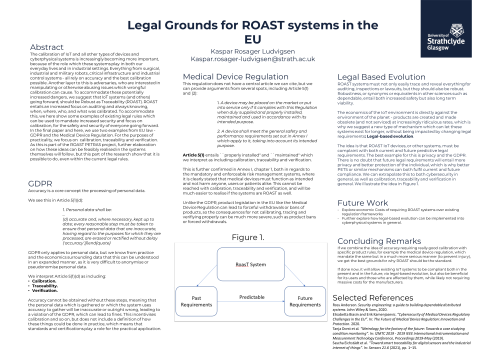
Ludvigsen, Nagaraja, Daly, YASM: Yet Another Surveillance Mechanism, https://arxiv.org/abs/2205.14601, 2022.
Ludvigsen, Nagaraja, The Opportunity to Regulate Cybersecurity in the EU (and the World): Recommendations for the Cybersecurity Resilience Act, http://arxiv.org/abs/2205.13196, 2022.
Shah, Ahmed, Nagaraja, Reconstructing Robot Operations via Radio-Frequency Side-Channel, https://arxiv.org/abs/2209.10179 , 2022
Shah, McIntee, Nagaraja, Bhandary, Arote, Kuri, Secure Calibration for Safety-Critical IoT: Traceability for Safety Resilience, https://arxiv.org/pdf/1908.00740.pdf, 2019.
Testbeds
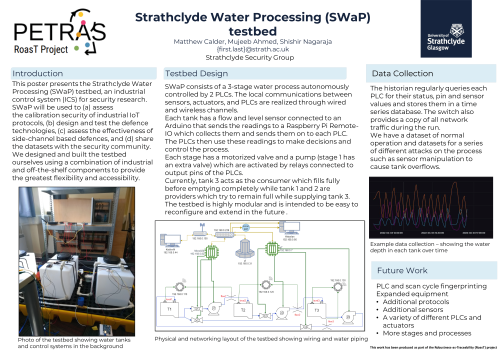
Simulated Water Treatment Plant Testbed in University of Newcastle.
The RoasT posters displayed at the PETRAS Academic Conference | Networking Research Showcase on 16 June 2022: