Health IoT Privacy and Security Transferred to Engineering Requirements (HIPSTER)
The HIPSTER project will help professional software developers in Health IoT, especially in small to medium companies, to address the trust, security and privacy needs of their systems in the most cost-effective way.
More than any other area of software development, IoT offers thorny and complex security, privacy and safeguarding (SPS) problems and requirements. In the health domain, these problems have a huge potential impact.
Yet protective Health IoT practices have been slow to emerge. In particular, developers working in teams in the Small-to-Medium Enterprise community are left relatively unsupported, without the benefit of existing knowledge of HIoT risks and threat probabilities. The resulting breaches will cause harm, and destroy trust in such systems, discouraging life improvements resulting from their adoption.
The research team will combine empirical research on software developers with cyber threat research discoveries to create a lightweight package of tools and workshops. These will enable development teams to assess their HIoT threats, assess their associated risks and impacts, identify business and corporate benefit from mitigating each, and hence support decision makers in prioritising SPS improvements against other software requirements. The package will of course incorporate evidence from the latest cyber threat intelligence in Health IoT.
Working with developer teams in their partner companies, the HIPSTER team will trial the package, and iteratively improve it. The materials will be open-sourced, and the team will promote them to the wider developer community through industry-focused events, social media, and support for developer teams using them.
By providing an easy-to-use, empowering approach that places developers as the creators of security, privacy and safeguarding solutions without the direct input of security professionals, the HIPSTER project will both increase security for users and promote UK-based innovations in the competitive Health IoT space.
Please click here to view the project webpage, and here to view the first blog relating to the research.
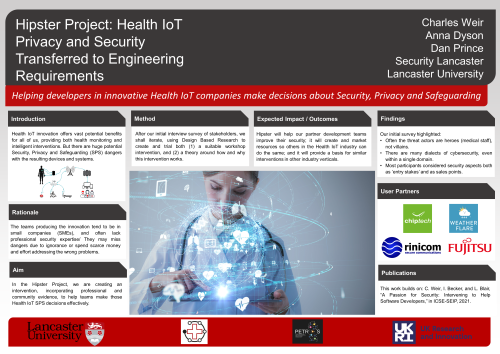
The HIPSTER poster displayed at the PETRAS Academic Conference | Networking Research Showcase on 16 June 2022:
The HIPSTER poster showcased two academic posters for the BASS23 Conference and the 2022 European Symposium on Usable Security. You can see the posters here and here.

